The actual tech for terms (Teleportation) that’s been overhyped by Hollywood movies. This is about how to prepare for when computers are 300X faster than the fastest today.
Overview
Quantum Supremacy
Quantum Supremacy is the point at which a quantum computer can complete a mathematical calculation that is demonstrably beyond the reach of even the most powerful supercomputer.
Quantum technologies are estimated to be 158 million times faster than the fastest supercomputer in 2022.
Estimates of 60 years would instead take seconds on a quantum computer.
Quantum can do in 4 minutes what traditional computers would take 10,000 years to do.
Quantum Cracking Risk Index?
The Quantum Cracking Risk Index metric is the average time to crack passwords and certificates for comparison of cracking methods.
This is different than https://standards.ieee.org/ieee/7131/10681/ which measures how fast a quantum computer works across various applications.
Our proposal: Identify the level of risk from quantum by periodically running a quantum secret-cracking tools against your organization’s passwords and certificates (given permissions to Vault, Active Directory, etc.).
Instead of an organization’s own live production Active Directory, perhaps a publicly available password database (dictionary for attack) could be used as the basis of a benchmark over time. Certs created by the maui.exe North Koreans are known to use to encrypt their ransomware targets’ data.
Quantum Spremacy means that such a metric is effective only if, over time, it provides an assessment even as quantum computers get faster.
The metric would inform corporate security mitigation policies such as:
“Require use of algorithms which generate cryptographic keys that can resist cracking longer than 2 years”.
This period means that the organization would have time to change all passwords and certificates in that period of time.
The recommendation for “from every 30-90 days to every 1-2 years” are based on “pre-quantum” estimates based on the use of “classical” computers (such as Windows) by adversaries.
Consideration of quantum capabilities is an extension of complexity policies (such as number of digits, special characters, etc.) that would be required to make a password meet the corporate threshold.
With quantum capabilities, the average time to crack keys is estimated to be much much shorter. Orders of magnitude shorter.
A NIST-published report from April 2016 cites experts that acknowledge the possibility of quantum technology to render the commonly used RSA algorithm insecure by 2030.
This benchmarking effort would also be the basis for measuring the capabilities of QC-resistant algorithms among Post-quantum cryptography (PQC) algorithms that take advantage of Atomic, Molecular, and Optical physics (AMO). NTRU is a finalist to NIST’s PQC competition. The name “NTRU” was originally derived from the pun Number Theorists ‘R’ Us or, alternatively, stood for Number Theory Research Unit1.
Other use cases
This means that quantum computers can solve problems that were impossible for traditional computers to solve, such as:
- Crack encryption cryptography (which can lead to stolen data)
- Simulate molecules (which can lead to new drugs)
- Optimize logistics (which can lead to more efficient supply chains)
- Optimize financial portfolios (which can lead to more efficient investments)
- Optimize machine learning (which can lead to more efficient AI)
QUOTE: Global market research and consulting company MarketsandMarkets estimates the global quantum computing market will grow from $866 million in 2023 at a compound annual growth rate of 38.3% to $4.375 billion in 2028. Another research company, P&S Intelligence, is even more optimistic and projects the market size to reach $65 billion by 2030.
Quantum machines are also great for optimization problems because they can crunch through vast numbers of potential solutions extremely fast. One of the most promising applications of quantum computers is for simulating the behavior of matter down to the molecular level. Quantum computers are also well-suited to accelerate artificial intelligence. They can crunch through millions of possibilities simultaneously, which could allow them to train deep-learning AI systems much faster than conventional computers can.
Actual instances reported:
- Airbus is using them to help calculate the most fuel-efficient ascent and descent paths for aircraft.
- Volkswagen has unveiled a service that calculates the optimal routes for buses and taxis in cities in order to minimize congestion.
- Daimler is using quantum computers to simulate the chemical composition of electrical-vehicle batteries to help find new ways to improve their performance.
- Pharmaceutical companies are leveraging them to analyze and compare compounds that could lead to the creation of new drugs.
IonQ’s analysis of usage type by key industries: https://ionq.com/industry-solutions/
Post-quantum schemes
VIDEO: “Post-quantum Cryptography” by Dimitri Va at github.com/VirgilSecurity
- 1978 Code-based cryptography
- 1979 Hash-based signatures
- 1996 Multivariate cryptography
- 2005 Lattice-based cryptography
- 2011 Supersingular isogeny key exchange
- 2022? Quantum key distribution?
A finalist in the NIST PQC competition is Falcon-512. It has a lattice-based signature scheme based on the problem of finding short integer solutions to a set of linear equations. It is relatively compact at 867-byte public key and 658-byte signature. It’s fast enough for constrained environments such as IoT devices at thousands per second.
Quantum Agility Index (QAI)?
Upcoming quantum capabilities imply that organizations now, more than ever, need to gear up to quickly change their security apparatus, especially to protect data at rest.
Just changing the frequency of password changes will be ineffective as well as annoying and disruptive.
Resisting quantum also means use of short-lived credentials throughout the infrastructure. That would include the use of Service Mesh (such as Istio) agents to handle communications, thus enabling new algorithms to be updated en masse, without changing code in the many programs handling business logic.
The Quantum Agility Index (QAI) KPI measures tracking how quickly each organization can quickly change its security apparatus throughout its tech stack. Specifically, the time between vendor announcement of availability to full implementation on all servers, desktops, laptops, and mobile devices?
- from one version to another of operating system such as Windows, Linux, macOS, iOS, Android, etc.
- from one version to another of a utility such as OpenSSL
- from one version to another of a programming library (as notified in GitHub Dependabots)
- from one version to another of a programming utility such as Brew, NPM, Maven, etc.
Others:
- from TLS 1.3 to TLS 1.X used by browsers on all servers and clients
- from SHA-1 to SHA-3 (Secure Hash Algorithm) to detect corruption on all file transfers
- from 2048-bit to 4096-bit keys on all servers and clients
- from RSA to ECC (Elliptic Curve Cryptography) algorithms to
- from AES-128 to AES-256 (Advanced Encryption Standard) algorithms to encrypt data at rest
- from X.509 version 3 to 4 on mTLS (mutual TLS) certificates within/outside Kubernetes
Increased agility also includes the generation of new certificates and passwords for each new session rather than reusing stale keys (such as SSH keys for accessing GitHub) that sit around waiting to be stolen.
To live safely in the post-quantum age, organizations need to be quick at switching to both larger password/certificate key lengths that take longer to crack and more advanced algorithms to generate keys.
Algorithmic Qubits (#AQ) Metric
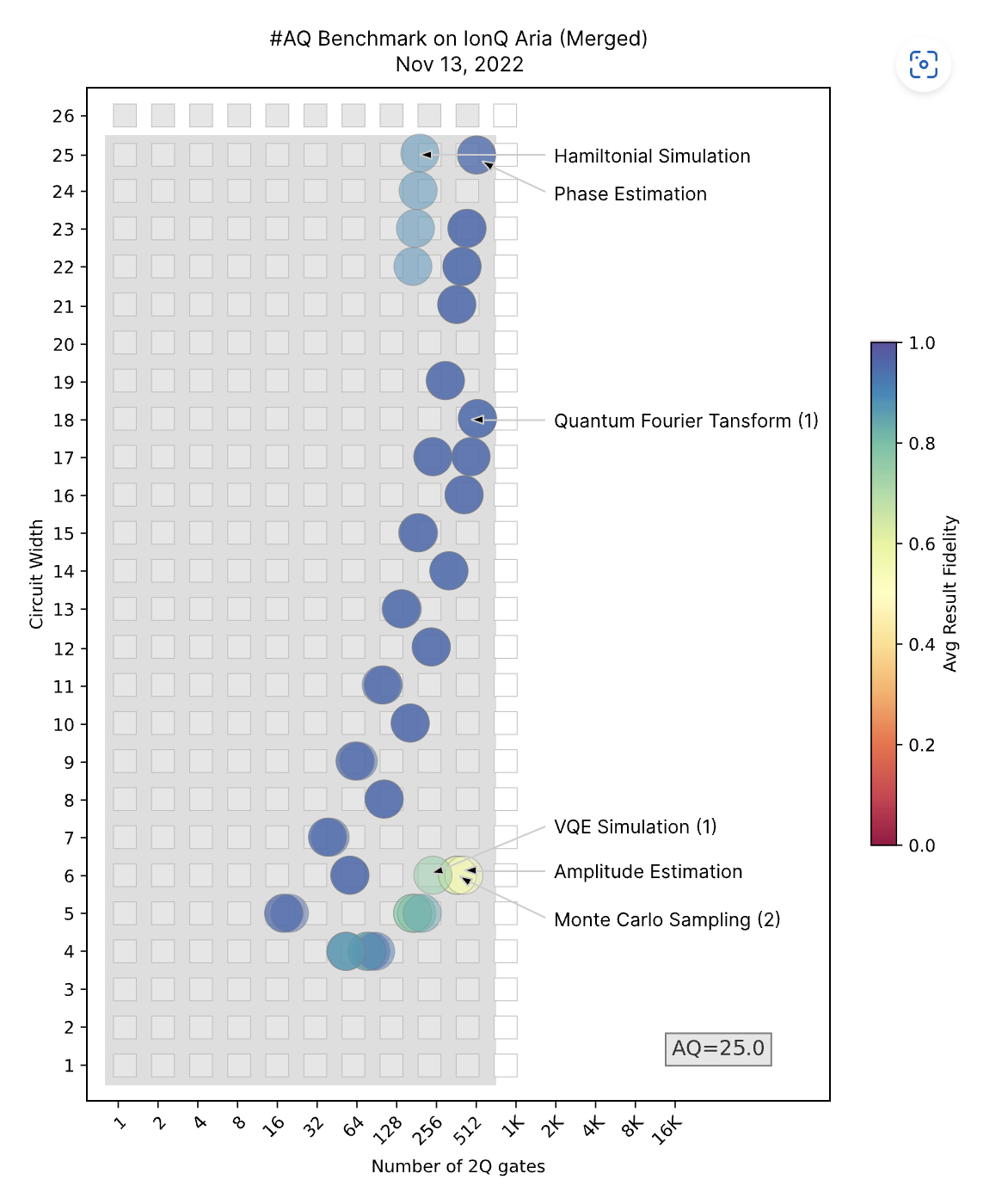
IonQ provides their Algorithmic Qubits (#AQ) metric to measure the effective number of qubits “2Q” needed to achieve fidelity on each given algorithm.
On the right, “Result Fidelity” measures how close the output of a quantum circuit is to the ideal output. The ideal output is the output that would be produced by a perfect quantum computer. The fidelity of a quantum circuit is a number between 0 and 1 (blue dots), where 1.0 represents perfect fidelity. “Success” can be defined along that spectrum, such as “37%”.
So the blue dots on the chart is saying that they have consistently achieved useful results across many (but not all) algorithms tested.
About “2Q”: Unlike IBM’s Quantum Volume (QV) metric, IonQ’s AQ adjusts down for error-correction resources in its number of “effectively perfect” qubits that are actually useful for a given algorithm. In the absence of error-correction encoding, AQ = log2(QV), or inversely, QV = 2AQ. AQ represents the number of “useful” encoded qubits in a particular quantum computer and is a simple proxy for the ability to execute real quantum algorithms for a given input size.
AQ is generally smaller than the number of physical qubits. Hence, ignore vendors (and by extension, their roadmaps) that describe their systems purely by the number of physical qubits. A 72 qubit chip and a million qubit chip with 95% fidelity gates both have a QV of 8 and an AQ of 3. With that fidelity, only three qubits can be used for calculation, no matter the number of physical qubits.
With conventional computers (such as Windows), doubling the number of bits doubles its processing power (a factorial increase). However, adding a qubit to a quantum machine produces an exponential increase in its number-crunching ability. Thus, a 30-qubit quantum machine would, in theory, be a million times more powerful than a 10-qubit one.
It’s unclear exactly how many qubits will be needed to achieve Quantum supremacy. Researchers keep finding new algorithms to boost the performance of classical machines, and supercomputing hardware keeps getting better. But researchers and companies are working hard to claim the title, running tests against some of the world’s most powerful supercomputers. IBM seeks a 1,000-qubit machine by 2023, up from 65 in 2020. A 1,000-qubit machine would still be 1000 times too small to break current internet encryption schemes. So IBM and Google plan to build a million-qubit quantum computer by 2030. IonQ plans to build a million-qubit machine by 2023.
Researchers Graig Gidney of Google, and Martin Ekera from the Swedish Royal Institute of Technology demonstrated that 20 million qubits could crack 2048-bit RSA in 8 hours. This is actually far better than previous estimates of 1 billion qubits would be needed to break 2048-bit RSA keys. The reason for the difference is that the new algorithm (based on the number field sieve) is much more efficient than previous algorithms.
The “Q” variable is called the “Hamiltonian” of a qubit-based system because the quantum dynamics of a physical system are determined by its “Hamiltonian” encoding of all information about the interactions between constituents of the system and the effects of exogenous driving forces in a 2N by 2N matrix of complex numbers on classical machines. By running Analog Hamiltonian Simulation (AHS) quantum tasks on a quantum device, one can avoid these exponential resource requirements. Special-purpose devices reproduce the time-dependent quantum dynamics of hundreds of simultaneously interacting qubits.
Quantum computers harness entangled qubits in a kind of quantum daisy chain. The machines’ ability to speed up calculations using quantum algorithms is why there’s so much buzz about their potential.
“Circuit Width” refers to techiques for optimizing circuits. Many quantum circuits can be made more efficient if they have access to ancilla bits used as a workspace. A single ancilla in an unknown (“dirty”) state can cut the cost of incrementing a register in half. A quantum register consists of multiple qubits taken together.
https://quantumai.google/cirq/hardware/azure-quantum/getting_started_ionq
Qubits
“Atom Computing claimed in 2023 to have built a 1,180 qubit quantum computer. While this is still too small to do real work, it’s the largest quantum computer we know about; it looks like it can scale to (somewhat) larger sizes; and it doesn’t require extreme cold.”
Adapted from Martin Giles January 29, 2019
“Classic” computers (such as Windows and Macs) work using bits — a stream of electrical or optical pulses representing 1s or 0s. Everything from tweets and e-mails to iTunes songs and YouTube videos are essentially long strings of these binary digits.
The secret to a quantum computer’s power lies in its ability to generate and manipulate quantum bits, or qubits.
Qubits are typically subatomic particles such as electrons or photons. Generating and managing qubits requires scientific and engineering breakthroughs in atomic, molecular, and optical physics (AMO). Most of the hardware of a quantum computer is to isolate qubits in a cold, controlled quantum state.
-
Companies such as IBM, Google, Microsoft, and Rigetti Computing, use superconducting circuits cooled to temperatures colder than deep space. Rigetti developed the pyQuil Python library and a quantum programming API.
-
IonQ traps individual atoms within electromagnetic fields on a silicon chip in ultra-high-vacuum chambers (what they call “trapped-ion technology”).
Qubits have quirky quantum properties such that a connected group of them can provide way more processing power than the same number of binary bits. One of those properties is known as superposition and another is called entanglement.
The quantum world is Probabilistic, not Deterministic. Matrices are used.
“If quantum mechanics hasn’t profoundly shocked you, you haven’t understood it yet.” - Niels Bohr
Superposition
Qubits can represent numerous possible combinations of 1 and 0 at the same time. This ability to simultaneously be in multiple states is called superposition.
To put qubits into superposition, researchers manipulate them using precision lasers or microwave beams.
This counterintuitive phenomenon is what enables a quantum computer with several qubits in superposition to crunch through a vast number of potential outcomes simultaneously. The final result of a calculation emerges only once the qubits are measured, which immediately causes their quantum state to “collapse” to either 1 or 0.
Entanglement
Researchers can generate pairs of qubits that are “entangled,” which means the two members of a pair exist in a single quantum state. Changing the state of one of the qubits will instantaneously change the state of the other one in a predictable way. Amazingly, this happens even if they are separated by very long distances.
Albert Einstein famously disparaged quantum entanglement as “spooky action at a distance,” because the idea that two particles separated by light-years could become “entangled” and instantaneously affect one another was counter to classical physics and intuitive reasoning.
Decoherence
The interaction of qubits with their environment in ways that cause their quantum behavior to decay and ultimately disappear is called decoherence. Their quantum state is extremely fragile. The slightest vibration or change in temperature—disturbances known as “noise” in quantum-speak—can cause them to tumble out of superposition before their job has been properly done. That’s why researchers do their best to protect qubits from the outside world in those supercooled fridges and vacuum chambers.
Early quantum devices are generally referred to as noisy intermediate-scale quantum (NISQ) devices.
Despite efforts, noise still causes lots of errors to creep into calculations. Smart quantum algorithms can compensate for some of these, and adding more qubits also helps. However, it will likely take thousands of standard qubits to create a single, highly reliable one, known as a “logical” qubit. This will sap a lot of a quantum computer’s computational capacity.
Sometimes described in technical specs as “T2 time,” coherence time is how long a qubit can maintain coherent phase, that is, how long it can successfully maintain one of the critical quantum qualities like superposition and entanglement necessary for computation. Without these, you could use the qubits like classical bits, but there wouldn’t be much utility in that. Again, ions have a major advantage over many other qubit technologies here, with coherence times measured in minutes, potentially thousands of times longer than other platforms.
Quantum Key Cracking tools
Cracking passwords and certificates using quantum computers requires hardware and software.
Quantum hardware manufacturers are also providing their own proprietary software running in public clouds:
- IBM Qiskit
- Google Cirq, led by Hartmut Neven
- Amazon Braket
- Microsoft Q# QML on Azure Quantum
Coding prototype volumetric benchmark algorithms (apps) used as the basis for AQ metrics are maintained by the Quantum Economic Development Consortium (QED-C) and SRI International. Their progress on each platform above is tracked in this table:
Notice that software used to crack passwords and certificates are not among them.
Cracking Software
VIDEO: Shor’s Algorithm is used to find the prime factors of an integer.
Run it in Jupyter on IBM’s Q System One quantum computers “quantum burglary” which calls Python qiskit to crack RSA encryption.
That’s the quantum equivalent of the Hashcat password-cracking tool using classic software and hardware (Windows).
Alternately, these CUDA running on NVDIA GPUs.
IBM Qiskit
https://quantum-computing.ibm.com/
https://www.research.ibm.com/ibm-q/network
IBM provides access to their actual quantum computers using IBMQ when it released its open-source quantum computing development environment called Qiskit.org (pronounced “kiss kit”) in 2017. It works with noisy quantum computers at the level of pulses, circuits, and algorithms.
IBM calls its jumbo liquid-helium refrigerator a “cryostat”.
Qiskit Textbook is a free introduction to quantum computing and Qiskit.
D-Wave
D-Wave at dwavesys.com is a Canadian firm that provides access to their quantum computers through their Leap cloud service.
Google Cirq
In 2018 Google announced the creation of a 72-qubit quantum chip called “Bristlecone”.
In 2021 Google has a cryogenic control circuit that operates at 4K, using Helium-4 and Helium-3 isotopes.
https://ai.google/research/teams/applied-science/quantum-ai/
- In Google Colab, Run this within Anaconda: https://github.com/smaranjitghose/quantum_burglary/blob/master/quantum_burglary.ipynb
- Get dependencies: pip install -r requirements.txt
- Run jupyter notebook quantum_burglary.ipynb
- Enter your message, encrypt it using RSA and watch Shor’s algorithm
Amazon Braket
Amazon provides a fully-managed IaaC service to quantum computers through their Amazon Braket offering [docs]. As with other AWS services, Braket jobs run under IAM policies and roles to control access to S3 storage buckets and other resources.
The “Braket” named after the “bra-ket” notation standard in quantum mechanics, aka Dirac notation introduced by Paul Dirac in 1939 to describe vectors (the state of quantum systems).
The Amazon Quantum Solutions Lab (AQSL) help customers explore the power of quantum computing and identify practical applications.
Amazon provides 1 free hour of simulation time per month on their Free Tier.
Access is provided through the AWS Braket GUI console or the AWS Braket SDK (Software Development Kit) for Python (braket.ahs), running in Jupyter notebooks on various providers of hardware and simulators.
AWS Braket enables use of the PennyLane open-source software library to assist with the variational quantum eigensolver (VQE) algorithm and approximate optimization algorithm (QAOA). (Eigen is German for “own” and used in Linear Algebra)
Microsoft QML (Quantum Machine Learning)
- Microsoft’s Quantum Computing Fundamentals Learning Path
- https://quantum.microsoft.com/ is the marketing landing zone
- https://learn.microsoft.com/en-us/azure/quantum/ is the documentation menu
- 2018 VIDEO by Dave Wecker on achieving practical quantum computing
- Install the Quantum Development Kit (QDK) on your local machine to develop and test quantum programs.
- Microsoft Quantum Team Blog
- Join the Microsoft Quantum Network to collaborate with Microsoft and other organizations on quantum computing.
In 2019, Microsoft developed a QDK (Quantum Development Kit) in Qiskit, Cirq, and Microsoft’s own Q# (Qsharp) languages that integrates with Python and .NET to run within Jupyter Kernel Type “IQ#” Notebooks running within Quantum workspaces in the Azure Quantum service that use Quantum simulators and QPUs (Quantum Processing Units) within hardware provided by:
-
Rigetti: Gate-based superconducting processors that utilize Quantum Intermediate Representation (QIR) to enable low latency and parallel execution. Simulator and QPU
-
IONQ: Dynamically reconfigurable trapped-ion quantum computer for up to 11 fully connected qubits, that lets you run a two-qubit gate between any pair.
-
Quantinuum: Trapped-ion system with high-fidelity, fully connected qubits, low error rates, qubit reuse, and the ability to perform mid-circuit measurements. Quantum simulators
-
Quantum Circuits, Inc: Full-stack superconducting circuits, with real-time feedback that enables error correction, encoding-agnostic entangling gates.
-
Pasqal: Neutral atom-based quantum processors operating at room temperature, with long coherence times and impressive qubit connectivity. You can pre-register today for Azure Quantum’s private preview of Pasqal.
Microsoft provides a $500 credit for each of these providers.
Others include IBM, D-Wave (a Canadian firm), Alibaba in China are also offering access to quantum machines.
Use the Azure Quantum Resource Estimator to estimate the cost of running your programs on these providers.
As with other Microsoft language architectures, a Quantum Intermediate Representation (QIR) program is produced from source code.
Install
-
View the Microsoft Quantum Development Kit (QDK) code repository:
https://github.com/microsoft/Quantum/
-
After installing az base, install the CLI extension
az extension add –upgrade -n quantum
-
There is a QDK extension for VS Code.
-
Install
pip install –upgrade azure-quantum
-
Install optional dependencies for submitting Qiskit programs:
pip install –upgrade azure-quantum[qiskit]
-
Install optional dependencies for submitting Cirq programs:
pip install –upgrade azure-quantum[cirq]
VSCode Project
-
Instead of creating new “Hello World” projects, clone the entire Microsoft Quantum Development Kit code repository at
git clone https://github.com/wilsonmar/DevSecOps.git –depth 1
-
In VSCode, open the folder “DevSecOps/Azure/QuantumHello”
-
Navigate to the folder “Quantum”, then “Samples” folder.
cd DevSecOps/Azure/QuantumHello
-
Verify the version of .NET Core you have installed:
dotnet --version
7.0.304 is the version I used at time of writing.
-
Run the “Hello World” program:
dotnet run
Visual Studio 2022 for Mac
-
https://devblogs.microsoft.com/visualstudio/tag/visual-studio-2022-for-mac/ says “Visual Studio 2022 for Mac” is in Preview (at time of writing Sep 2023).
-
If you have a Mac machine containing Apple Silicon (ARM64) M1 & M2 processors, at https://learn.microsoft.com/en-us/visualstudio/releases/2022/mac-release-notes click the blue “Download” for the latest Visual Studio 2022 for Mac installer, such as 50 MB “visualstudioformacinstaller-17.6.0.49.dmg”.
NOTE: That installs a different product than brew install –cask visual-studio which installs product “Visual Studio for Mac” (at version 17.5) is scheduled for retirement on August 31, 2024.
WARNING: Do not download file VisualStudioSetup.exe for Windows PCs from https://visualstudio.microsoft.com/vs/mac/
It contains .NET 6.0 SDKs.
-
In your Finder, double-click “visualstudioformacinstaller-17.6.0.49.dmg” to run it.
- Double-click the “Install” button. Click “Open” on the confirmation pop-ups.
- Click “Install and Update” with a check to install 3.5 GB containing .NET Core 7 SDK (the 3.1 has been deprecated)
- Provide your Mac password to allow the installation. A few times.
- Click “Continue” to install 1.5 GB of .NET 6.0 SDKs.
- When “Done” appears, squeeze 4 fingers together on your mac trackpad to view apps.
- Click the “Visual Studio 2022 (preview).app” icon to run it.
- Click the “X” to close the installer dialog.
- In Finder, Downloads, right-click the “Visual Studio 2022 (preview).app” to Move it to trash.
Q# (Qsharp) Programming
https://docs.microsoft.com/azure/quantum/concepts-overview/
https://docs.microsoft.com/azure/quantum/concepts-qsharp-fundamentals/
See Q# code samples using the QDK.
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/intro-to-qsharp-jupyter/
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/running-your-first-job-on-the-azure-quantum-service/
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/run-q-programs-from-python-or-net/ using code at https://github.com/microsoft/quantum/tree/main/samples/interoperability/qrng
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/creating-random-numbers-with-quantum-computing/
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/solving-sudoku-using-grovers-algorithm/
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/qsharp-with-dotnet/
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/visualization/
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/facts-and-assertions/
- https://learn.microsoft.com/en-us/samples/microsoft/quantum/quantum-teleportation-sample/ of entangled quibits See 1,400 km (870 mi)
CAUTION: Azure Quantum and the QDK manage three different capability profiles for QPU hardware:
-
Full: This profile can run any Q# program within the limits of memory for simulators or the number of qubits for physical quantum computers. Try it using the Full state simulator.
-
No Control Flow: This profile can run any Q# program that doesn’t require the use of results from qubit measurements that control program flow. Within a Q# program targeted for this kind of QPU, values of type Result don’t support equality comparison, such as this comparison between two results (desired != M(q)) to control the computation flow with an if statement:
operation SetQubitState(desired : Result, q : Qubit) : Result {
if (desired != M(q)) {
X(q);
}
}
operation MeasureQubit(q : Qubit) : Result {
return M(q);
}
operation SampleMeasuredQubit(q : Qubit) : Result {
H(MeasureQubit(q));
return M(MeasureQubit(q));
}
- Basic Measurement Feedback profiles have limited ability to use the results from qubit measurements to control the program flow. Within a Q# program targeted for this kind of QPU, you can compare values of type Result as part of conditions within if statements in operations, allowing mid-circuit measurement.
Basic Measurement Feedback profile targets allow measurement-based conditional operations and mid-circuit measurements, meaning that qubits can be selectively measured at a point other than the final statement of a quantum program, and the output of the measurement can be used in other operations. Mid-circuit measurement enables multiple measurements at any point throughout the quantum program. The quantum information of the measured qubits collapses to a classical state (zero or one), but the non-measured qubits retain their quantum state.
operation MeasureQubit(q : Qubit) : Result {
return M(q);
}
operation SetToZero(q : Qubit) : Unit {
if MeasureQubit(q) == One { X(q); )
}
Notice corresponding conditional blocks might not contain return or set statements.
Honeywell
Honeywell has a relationship with Microsoft.
Cambridge Quantum Computing
Rigetti
Circuit diagrams
QASM (Quantum Assembly Language) is a textual representation of quantum circuits.
Graphical depiction of quantum circuit elements is described using a variant of the Penrose graphical notation. Richard Feynman used an early version of the quantum circuit notation in 1986.
Each horizontal line (left to right) represents time for a qubit. Doubled lines represent classical bits.
Items connected by lines are operations performed on the qubits, such as measurements or gates.
These lines define the sequence of events, and are usually not physical cables.
The “depth” of a circuit is a metric that calculates the longest path between the data input and the output. Each gate counts as a unit.
The simplest gate involves one qubit, called a Hadamard Gate (H) which puts the qubit into superposition (flipping the qubit from 0 to 1 or vice versa). It’s also known as a square-root of NOT gate. The Pauli-X gate (NOT gate)…
| The CNOT gate (controlled-NOT gate) is a two-qubit gate that performs a NOT operation on the second qubit only when the first qubit is in the state | 1⟩. |
The “width” of a circuit is the number of qubits used.
A gate that operates on two qubits is called a Controlled-NOT (CN) Gate.
A gate that operates on three qubits is called a Controlled Controlled-NOT (CCN) Gate.
References
https://learn.microsoft.com/en-us/visualstudio/mac/supported-versions-net?view=vsmac-2022&WT.mc_id=dotnet-35129-website
https://dotnet.microsoft.com/download/dotnet/3.1?azure-portal=true
https://dotnet.microsoft.com/en-us/download/dotnet/7.0
dotnet-sdk-7.0.401-osx-x64.pkg
https://download.visualstudio.microsoft.com/download/pr/e0f9aead-ae21-411b-bb38-1c6393fb278a/69566da6d19724215edda3af6a9663cd/dotnet-sdk-7.0.401-osx-x64.pkg
-
Install .NET SDK 6.0 from https://dotnet.microsoft.com/download
-
Create a quantum-based random number generator (project “QuantumRNG”)
https://learn.microsoft.com/en-us/azure/quantum/quickstart-microsoft-qc?pivots=platform-ionqTUTORIAL: https://learn.microsoft.com/en-us/training/modules/qsharp-create-first-quantum-development-kit/
-
Project file QuantumRNG.csproj
<Project Sdk="Microsoft.Quantum.Sdk"> <PropertyGroup> <OutputType>Exe</OutputType> <TargetFramework>net6.0</TargetFramework> <ExecutionTarget>ionq.qpu</ExecutionTarget> </PropertyGroup> </Project>
-
Starter code “Program.qs” (Q#):
namespace QuantumRNG { open Microsoft.Quantum.Intrinsic; open Microsoft.Quantum.Measurement; open Microsoft.Quantum.Canon; @EntryPoint() operation GenerateRandomBits() : Result[] { use qubits = Qubit[4]; ApplyToEach(H, qubits); return MultiM(qubits); } } -
Run on IonQ, Quantinuum, and Rigetti.
-
quantum gates, algorithms, and T factories (Toffoli, Fredkin, etc.)
Error correction is necessary.
s input and, therefore, supports any language that translates to QIR, for example, you can use the Azure Quantum Resource Estimator with Q# and Qiskit.
Examples of problems that can use this approach are Variational Quantum Eigensolvers (VQE) and Quantum Approximate Optimization Algorithms (QAOA).
The Azure Quantum Resource Estimator computes post-layout physical resource estimation by taking a set of inputs such as qubit parameters, the quantum error correction (QEC) code, the error budget, and other parameters into account. It takes a Quantum Intermediate Representation (QIR) program as input and, therefore, supports any language that translates to QIR, for example, you can use the Azure Quantum Resource Estimator with Q# and Qiskit.
https://www.technologyreview.com/s/612844/what-is-quantum-computing/?utm_campaign=site_visitor.unpaid.engagement&utm_source=hs_email&utm_medium=email&utm_content=69704878&_hsenc=p2ANqtz-_1ri8lmxU5s3GtYayE9BTUjc9X24kky1mK95qgkzX5HOWJ9Jq4cwe80r50ZMkk68XKiRgqhZKDz3cfYtQpOmv2FC4_Fw&_hsmi=69704878
Nano tech
Nano-switches made out of graphene could make electronics even smaller. China’s military is rushing to use artificial intelligence. Even Amazon wants face recognition regulated. China is leaving the US in the dust on electric-vehicle chargers.
Universities and businesses working on them are facing a shortage of skilled researchers in the field—and a lack of suppliers of some key components.
If these exotic new computing machines live up to their promise, they could transform entire industries and turbocharge global innovation.
Event builder Meet with David Mendies
Resources
-
https://ionq.com/resources/glossary
-
NIST Post-Quantum Computing Standard https://www.nist.gov/newsevents/ news/2019/01/nist-reveals-26-algorithms-advancing-post-quantum-crypto-semifinals
-
OReilly: Quantum Computing in Action</a> Manning Publications February 2022 By Johan Vos
-
8-Hour video “Quantum Computing Fundamentals” on OReilly from Pearson February 2023 - introduction to Quantum Computing from Dr. Chuck Easttom at Vanderbilt and Georgetown.
-
https://quantumcomputing.stackexchange.com/questions/5769/how-to-calculate-circuit-depth-properly
-
https://www.classiq.io/docs/constraints
https://sdtimes.com/softwaredev/mastering-the-quantum-code-a-primer-on-quantum-software/
BLOG: https://security.apple.com/blog/imessage-pq3/ https://www.youtube.com/watch?v=4USgxax1-RQ Apple Updates iMessage with Post Quantum Encryption (PQC) https://signal.org/blog/pqxdh/ Signal protocol published in 2013 https://signal.org/docs/specifications/x3dh/ X3DH Key Agreement Protocol HNDL forward secrecy